Palo Alto, Calif. — Smart watches have significant security flaws, HP found in testing 10 devices.
All of them “contain significant vulnerabilities, including insufficient authentication, lack of encryption and privacy concerns,” the company’s HP Fortify security group said. The security issues could enable hackers to get unauthorized access to a smart watch’s stored health data and deliver unauthorized access to connected homes and cars, HP warned.
“Smart watches have only just started to become a part of our lives, but they deliver a new level of functionality that could potentially open the door to new threats to sensitive information and activities,” said Jason Schmitt, general manager of HP Fortify. “As the adoption of smart watches accelerates, the platform will become vastly more attractive to those who would abuse that access, making it critical that we take precautions when transmitting personal data or connecting smart watches into corporate networks.”
HP recommends that users not enable a smart watch’s car- and home-control functions unless strong authorization is offered. “In addition, enabling passcode functionality, ensuring strong passwords and instituting two-factor authentication will help prevent unauthorized access to data,” HP said. HP’s full report outlines guidelines for secure smart-watch use.
The most common — and easily addressable — security issues, HP said, include:
- Insufficient User Authentication/Authorization: Every tested smart watch was paired with a phone interface that lacked two-factor authentication and the ability to lock out accounts after three to five failed password attempts. Three of the 10 were vulnerable to “account harvesting,” meaning an attacker could access the device and its data via a combination of weak password policy, lack of account lockout, and user enumeration. The latter vulnerability enables hackers to identify user accounts through feedback received from reset password mechanisms.
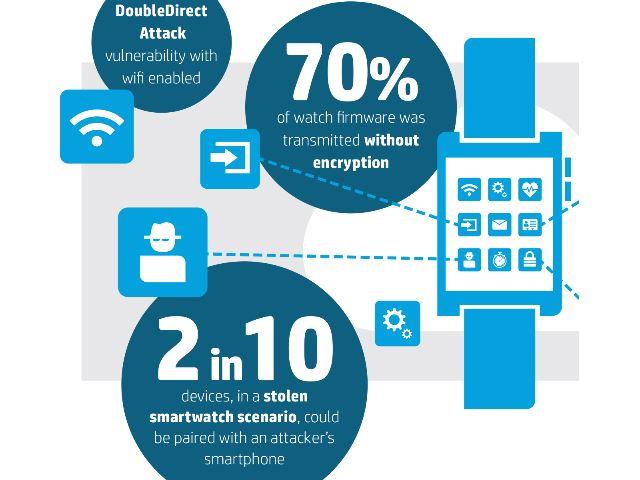
- Lack of transport encryption: All of the tested products implemented transport encryption using SSL/TLS, but 40 percent of the cloud connections were vulnerable to the Poodle attack, allowed the use of weak cyphers, or still used SSL v2.
- Insecure interfaces: Thirty percent of the tested smart watches used Cloud-based web interfaces, all of which exhibited “account-enumeration concerns.” In a separate test, 30 percent also exhibited account enumeration concerns with their mobile applications.
- Insecure software/firmware: A full 70 percent of the smart watches presented concerns with their protection of firmware updates, including transmitting firmware updates without encryption and without encrypting the update files. Although many updates were designed to prevent the installation of contaminated firmware, the lack of encryption allows the files to be downloaded and analyzed.
- Privacy concerns: All smart watches collected some form of personal information, such as name, address, date of birth, weight, gender, heart rate and other health information. “Given the account enumeration issues and use of weak passwords on some products, exposure of this personal information is a concern,” HP said.












